The cryptocurrency landscape offers exciting opportunities, but it comes with significant security risks. As digital assets gain mainstream adoption, hackers and scammers increasingly target crypto exchanges and their users. In 2023 alone, hackers stole over $2.38 billion in cryptocurrency through various attacks. This comprehensive guide will equip you with essential security practices to protect your digital assets when using cryptocurrency exchanges in 2024.
Understanding Cryptocurrency Exchange Security
Cryptocurrency exchanges are platforms where users can buy, sell, and trade digital assets. While these platforms implement various security measures, the responsibility for protecting your assets ultimately falls on you. Understanding the security landscape is the first step toward safeguarding your investments.
Common Security Threats
- Phishing attacks targeting exchange credentials
- SIM swapping to bypass two-factor authentication
- Exchange hacks and infrastructure breaches
- Malware designed to steal private keys
- Social engineering scams on social media

Recent Example: In September 2023, Mixin Network suffered a $200 million hack when attackers exploited a vulnerability in their database. This incident highlights the importance of not keeping all your assets on a single exchange.
10 Essential Security Practices for Cryptocurrency Exchanges
Implementing these security measures will significantly reduce your risk when using cryptocurrency exchanges. Each practice adds an extra layer of protection to your digital assets.

1. Use Strong, Unique Passwords
Your first line of defense is a strong password. Create complex passwords that include uppercase and lowercase letters, numbers, and special characters. Most importantly, use a different password for each exchange account.
“Using the same password across multiple platforms is like using the same key for your house, car, and office. If one gets compromised, everything is at risk.”
Pro Tip: Use a reputable password manager like Bitwarden or 1Password to generate and store complex passwords securely. This allows you to create unique passwords for each platform without having to remember them all.
2. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security by requiring a second verification method beyond your password. This significantly reduces the risk of unauthorized access, even if your password is compromised.
| 2FA Method | Security Level | Pros | Cons |
| SMS Codes | Low | Easy to set up | Vulnerable to SIM swapping attacks |
| Email Codes | Medium | Convenient | Vulnerable if email is compromised |
| Authenticator Apps | High | Works offline, time-based codes | Requires smartphone access |
| Hardware Keys | Very High | Physical device required, highly secure | Cost, can be lost or damaged |
Enhance Your Security with a Hardware Key
For maximum protection, consider investing in a hardware security key like YubiKey or Trezor for your 2FA needs.
3. Use Cold Storage for Long-Term Holdings
Cold storage refers to keeping your cryptocurrency offline, away from internet-connected devices. This approach significantly reduces the risk of online attacks and unauthorized access.
For long-term investments, consider moving your assets to:
- Hardware wallets like Ledger or Trezor that store private keys offline
- Paper wallets with printed public and private keys (though less convenient)
- Air-gapped computers that have never connected to the internet
Only keep the amount you need for active trading on exchanges. A good rule of thumb is to keep no more than 5-10% of your total holdings on exchanges.

4. Verify Exchange Security Measures
Not all cryptocurrency exchanges offer the same level of security. Before choosing an exchange, research their security practices and history.

Look for exchanges that implement:
- Majority of funds stored in cold storage (ideally 95%+)
- Regular security audits by reputable firms
- Insurance coverage for digital assets
- Transparent security practices and incident response
- Compliance with relevant regulations
Warning: In July 2023, Multichain lost $130 million when a former developer allegedly compromised private keys. Always research an exchange’s security history and leadership before entrusting them with significant assets.
5. Be Vigilant Against Phishing Attempts
Phishing remains one of the most common ways hackers gain access to cryptocurrency accounts. These attacks typically involve fake websites, emails, or messages designed to steal your login credentials or private keys.

Protect yourself by:
- Always double-checking website URLs before entering credentials
- Bookmarking official exchange websites instead of using search engines
- Never clicking on links in emails claiming to be from exchanges
- Verifying email sender addresses carefully
- Being suspicious of urgent requests or too-good-to-be-true offers
Stay Updated on Latest Phishing Techniques
Subscribe to our newsletter for regular updates on the latest cryptocurrency security threats and how to avoid them.
Advanced Security Measures for Experienced Users
If you’re an experienced cryptocurrency user with significant holdings, consider implementing these additional security measures for maximum protection.
6. Use a Dedicated Device for Crypto Transactions
Consider using a separate computer or mobile device exclusively for cryptocurrency transactions. This device should have minimal software installed, regular updates, and strong antivirus protection.

7. Implement IP and Withdrawal Address Whitelisting
Many exchanges allow you to restrict account access to specific IP addresses and limit withdrawals to pre-approved wallet addresses. This prevents unauthorized transfers even if someone gains access to your account.
“Whitelisting withdrawal addresses is like having a pre-approved list of recipients for your bank transfers. Even if someone gets your account credentials, they can’t send funds to addresses not on your list.”
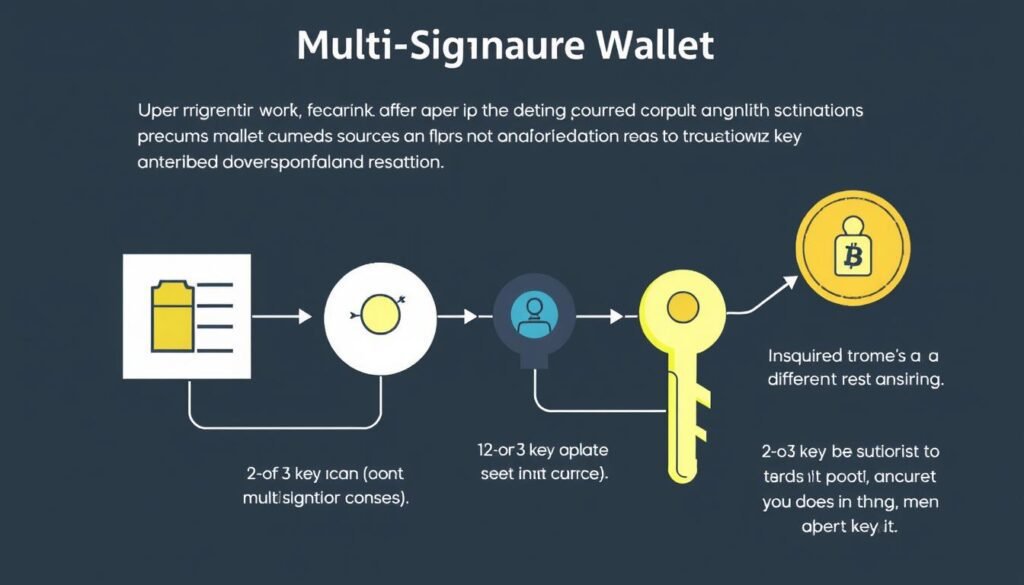
8. Use Multi-Signature Wallets
Multi-signature (multisig) wallets require multiple private keys to authorize a transaction. This creates redundancy and prevents a single point of failure in your security setup.
For example, you might set up a 2-of-3 multisig wallet where keys are stored on different devices or with trusted individuals. This means any transaction would require at least two of the three keys to be approved.
9. Regular Security Audits of Your Setup
Periodically review your entire cryptocurrency security setup. This includes checking for software updates, reviewing account access logs, and testing your recovery procedures.
| Security Check | Frequency | What to Look For |
| Password review | Every 3 months | Password strength, uniqueness across platforms |
| Account access logs | Weekly | Unfamiliar IP addresses, unusual login times |
| Software updates | Monthly | Latest versions of wallets, authenticator apps |
| Recovery process test | Every 6 months | Verify seed phrases work, backup accessibility |
| Full security audit | Yearly | Comprehensive review of all security measures |
10. Stay Informed About Security Developments
The cryptocurrency security landscape evolves rapidly. Stay updated on the latest threats, vulnerabilities, and best practices by following reputable security resources.
- Subscribe to security newsletters from trusted exchanges
- Follow cryptocurrency security experts on social media
- Join community forums focused on crypto security
- Read security audits and post-mortems of exchange hacks
Centralized vs. Decentralized Exchanges: Security Comparison
Understanding the security differences between centralized exchanges (CEX) and decentralized exchanges (DEX) can help you make informed decisions about where to trade your assets.
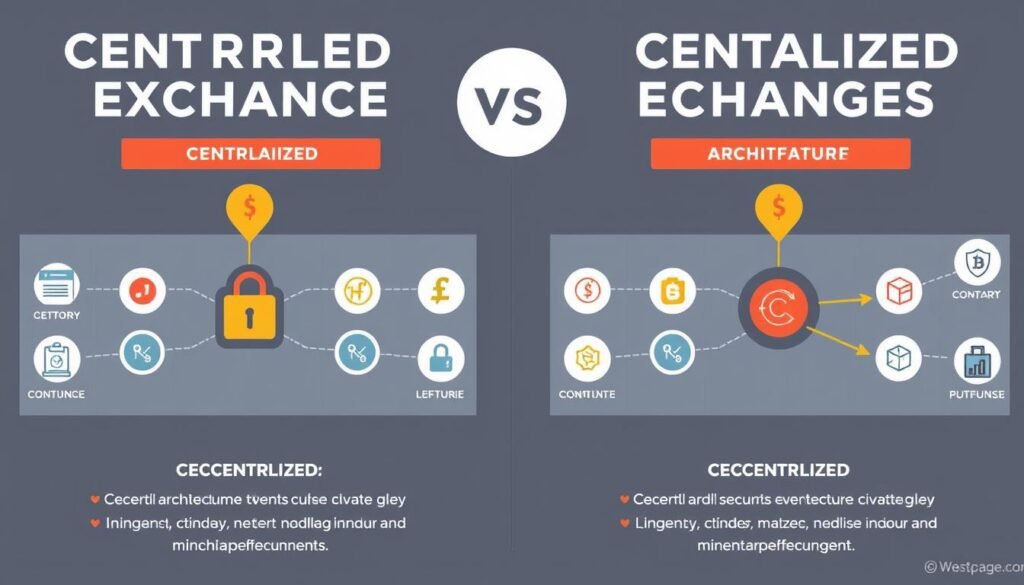
- Custody of your assets held by the exchange
- Usually offer insurance and customer support
- More user-friendly interfaces
- Higher liquidity and trading volume
- Vulnerable to company-wide hacks
- Subject to regulatory oversight
Centralized Exchanges (CEX)
- You maintain custody of your assets
- No central point of failure
- Often more private with fewer KYC requirements
- Smart contract risks instead of company risks
- Generally less user-friendly
- Lower liquidity for some assets
Decentralized Exchanges (DEX)
“The key security difference is custody. With CEXs, you’re trusting the exchange to secure your assets. With DEXs, you’re responsible for your own security, but don’t face custodial risk.”
For optimal security, consider using a combination approach:
- Use reputable centralized exchanges for fiat on/off ramps and high-liquidity trading
- Use decentralized exchanges for maintaining control of assets during trades
- Always move significant holdings to cold storage after trading
Real-world Example: In March 2023, Euler Finance lost $197 million in a flash loan attack on their DeFi protocol. While decentralized platforms remove custodial risk, they introduce smart contract vulnerabilities that can be equally devastating.
Learning from Major Exchange Hacks (2019-2024)
Examining past security breaches provides valuable lessons for protecting your assets. Here are some significant exchange hacks and the key takeaways from each.
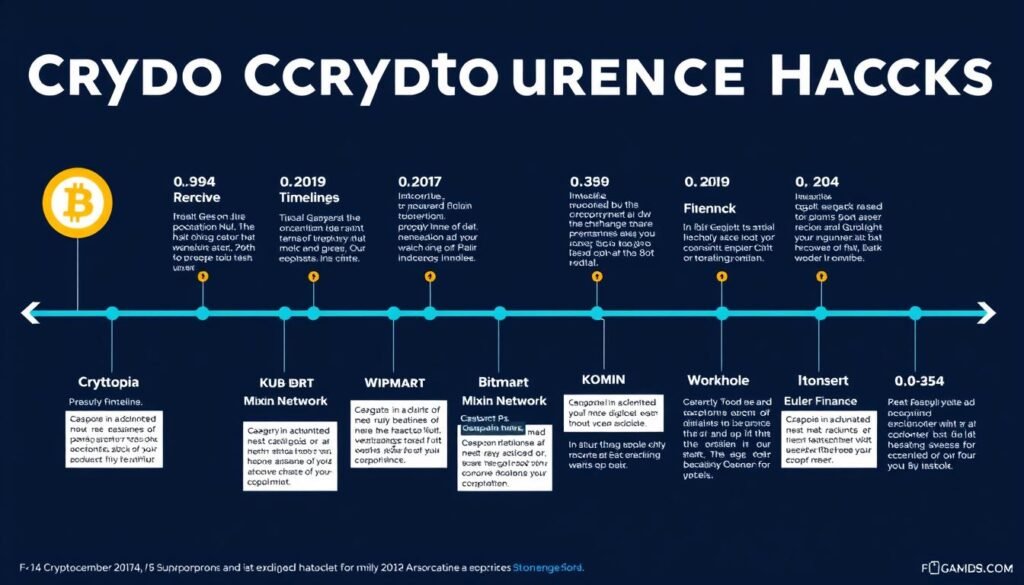
Binance Hack (May 2019)
Hackers stole 7,000 Bitcoin (worth $40 million at the time) by obtaining API keys, two-factor codes, and other user information.
Key Lessons:
- Limit API access permissions
- Use hardware-based 2FA when possible
- Enable withdrawal address whitelisting
KuCoin Hack (September 2020)
Attackers compromised the exchange’s hot wallets, stealing approximately $280 million in various cryptocurrencies.
Key Lessons:
- Exchanges should keep minimal funds in hot wallets
- Users should withdraw to personal wallets after trading
- The importance of exchange insurance funds
Bitmart Hack (December 2021)
Hackers stole approximately $200 million after compromising a private key to the exchange’s hot wallets.
Key Lessons:
- Private key management is critical
- Multi-signature wallets add necessary redundancy
- Diversify holdings across multiple secure platforms
Mixin Network Hack (September 2023)
Attackers exploited a database vulnerability to steal $200 million in various cryptocurrencies.
Key Lessons:
- Infrastructure security is as important as wallet security
- Regular security audits are essential
- Consider the security history of platforms before using them
Pattern Recognition: Many major hacks involve compromised private keys or hot wallet vulnerabilities. This reinforces the importance of cold storage for long-term holdings and careful selection of exchanges based on their security practices.
Frequently Asked Questions
Are cryptocurrency exchanges safe to use?
Cryptocurrency exchanges vary widely in their security practices. Reputable exchanges implement multiple layers of protection, including cold storage, encryption, and regular security audits. However, no exchange is 100% secure. Best practice is to use exchanges only for trading and move significant holdings to personal wallets that you control.
What should I do if I suspect my exchange account has been compromised?
If you suspect a security breach:
- Immediately change your password from a secure device
- Disable API keys and revoke any third-party access
- Enable or reset two-factor authentication
- Contact the exchange’s support team immediately
- Monitor your account for unauthorized transactions
- Consider freezing withdrawals if the exchange offers this feature
How can I recover stolen cryptocurrency?
Unfortunately, recovering stolen cryptocurrency is extremely difficult due to the irreversible nature of blockchain transactions. Your best options are:
- Report the theft to the exchange immediately
- File a police report with transaction details
- Contact blockchain analytics firms that specialize in tracking stolen funds
- Check if the exchange has an insurance fund that covers losses
Prevention is much more effective than attempting recovery after a theft.
Which cryptocurrency wallets are most secure?
Hardware wallets generally offer the highest security for cryptocurrency storage. Popular options include:
- Ledger Nano X and Nano S Plus
- Trezor Model T and Trezor One
- KeepKey
- BitBox02
These devices store your private keys offline, protecting them from online attacks while still allowing you to send and receive transactions when needed.
Is it safe to keep cryptocurrency on exchanges long-term?
Keeping large amounts of cryptocurrency on exchanges for extended periods is generally not recommended. Exchanges are prime targets for hackers, and even the most secure platforms can be vulnerable. The crypto community follows the principle: “Not your keys, not your coins,” emphasizing that true ownership requires control of private keys. For long-term holdings, transfer assets to a hardware wallet or other secure cold storage solution.
Conclusion: Building Your Cryptocurrency Security Strategy
Securing your assets when using cryptocurrency exchanges requires a multi-layered approach. By implementing the practices outlined in this guide, you can significantly reduce your risk exposure while still enjoying the benefits of digital asset trading.
Remember these key principles:
- Use strong authentication methods, including hardware-based 2FA when possible
- Keep the majority of your holdings in cold storage
- Diversify across multiple secure solutions rather than relying on a single platform
- Stay vigilant against phishing and social engineering attempts
- Regularly audit your security setup and stay informed about emerging threats
The cryptocurrency space continues to evolve, and so do the security challenges. By staying informed and implementing best practices, you can protect your digital assets and enjoy greater peace of mind.
Download Our Complete Cryptocurrency Security Checklist
Get our comprehensive security checklist to ensure you’ve covered all aspects of cryptocurrency exchange security. This printable PDF includes all the tips from this article plus additional advanced security measures.

